Hello everyone! I’m thrilled to introduce the Intrusio Firewall Project, an exciting new initiative that’s currently in development. Our goal with Intrusio is to provide an easy-to-use, cost-effective […]
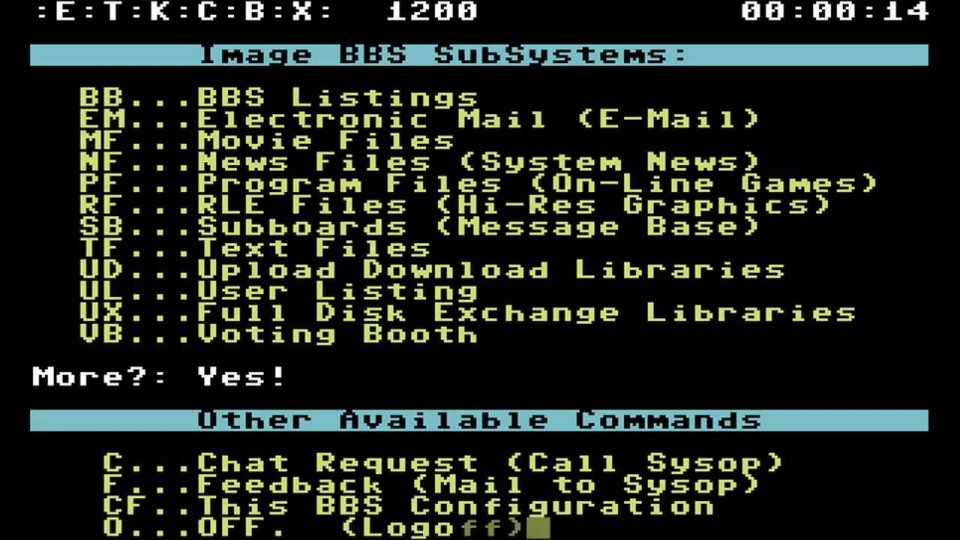
From Warez to Torrents: A Journey Through the Shadows of the Internet
There’s a certain nostalgia that comes with remembering the early days of the internet, especially if you were around during the wild west era of warez and torrents. […]
Python3 LAN host detection using Scapy
This simple setup helps you keep track of devices on your network by running a background script that scans for new hosts every 30 seconds. If a new […]
Intrusio Updates: Day 1
Yesterday was a productive day as I managed to get Free Range Routing (FRR) integrated into the Intrusio build script. This means that Intrusio now has built-in support […]
Integrating BGP Tools & Shodan’s Internet DB
Overview This was a bit of experimenting using bgptools & shodan to try see if i could get a quick way of assessing a block of IP’s or […]
Sending Emails with Python and SendGrid: A Quick Guide
Hey folks! 🖐 Ever wanted to send emails from your Python scripts but didn’t know where to start? I recently dove into this and thought I’d share a […]
Introduction to Mikrotik Router Configuration with Python
Mikrotik routers are powerful and versatile devices widely used in both home and enterprise environments. While the RouterOS interface is quite intuitive, automating configurations using Python can significantly […]
Exploring the Match Feature in Python 3.10
Python 3.10 introduced several new features aimed at enhancing productivity and code readability. Among these, the match statement stands out as one of the most significant additions, offering a powerful […]
Python – Simple Nested Execution (Naughty)
Recently, i was exploring the use case of having python trigger a dynamic ‘python’ payload on the fly with no knowledge of what the payload might contain, other […]